Government communication systems are now battlegrounds as critical as territorial borders. Every day, state adversaries, cybercriminals, and rogue actors probe them for weaknesses—knowing that a single intercepted exchange can derail negotiations, compromise operations, or erode public trust. The scale of exposure is sobering: global cybercrime costs are projected to exceed $1.2 trillion annually by 2025, much of it tied to espionage and state-backed incursions into public infrastructure. In Australia alone, espionage inflicted over AU $12.5 billion in damage during 2023–24; while mitigations saved tens of billions, the cost of unsecured communication remains a national liability.
Despite these risks, most governments still rely on commercial platforms and generic collaboration tools. While these may provide surface-level encryption, they are not engineered for sovereign-grade resilience. They leave three critical gaps: loss of sovereign control, lack of intelligence augmentation, and insufficient decision-making support. In practice, this mismatch between the threat landscape and available tools increases exposure, slows coordination, and undermines trust.
Addressing this requires more than secure channels. It requires a sovereign communication backbone—built on military-grade encrypted overlays and enhanced with agentic AI operating entirely within national infrastructure. Such a platform does more than defend: it actively supports governance, distilling vast streams of information into actionable insights, surfacing compliance and policy risks, and enabling leaders to act with speed, clarity, and confidence.
The Problem We’re Solving
Governments face a structural communication gap that cannot be bridged by commercial collaboration tools or conventional secure messaging. This gap manifests in three interrelated challenges:
1. National Security Threats
Cyberattacks on sovereign communication systems have grown by over 300% in the past decade, with intelligence leaks, intercepted ministerial chats, and disrupted negotiations now routine elements of hybrid warfare. Each breach carries severe consequences—compromised national security, economic losses, and weakened public trust. Commercial apps, built for convenience and scale, were never designed to withstand state-level adversaries or ensure sovereign custodial control.
2. Operational Fragmentation
Effective governance requires coordination across ministries that manage defense, health, infrastructure, energy, and foreign affairs. Yet these institutions typically operate in silos, with data trapped in departmental systems. In moments of crisis—pandemics, cyberattacks, natural disasters—the inability to share insights quickly can translate into billions in economic damage or even the loss of lives. Fragmented communication is no longer just inefficient; it is a strategic vulnerability.
3. Cognitive Overload
Senior officials process hundreds of messages, calls, and documents every week, spread across multiple disconnected platforms. This deluge dilutes clarity, slows critical decisions, and undermines accountability. Without intelligent systems to distill and direct information, leaders risk decision paralysis, where the weight of data obstructs timely, effective action.
The consequence is clear: governments are more vulnerable, slower to respond, and less trusted by citizens. Addressing this requires a sovereign communication system that not only defends against external threats, but also integrates cross-ministry workflows and augments human judgment at scale.
Value Proposition
This platform is not another encrypted chat tool; it is a sovereign communication backbone, engineered to combine military-grade security with agentic AI intelligence. Its architecture is explicitly designed to address the structural weaknesses governments face in securing, integrating, and governing information flows at scale.
Military-Grade Security: Built on an encrypted overlay network with custodial key management and private federation, the system ensures that no external entity—state or non-state—can intercept or surveil communications. Encryption keys are state assets, not vendor-managed, establishing an environment resilient against nation-state adversaries and hybrid warfare tactics.
Agentic Intelligence: The embedded AI agent functions as an active participant, not a passive assistant. It summarizes live discussions, detects patterns across ministries, flags compliance risks, and proactively prompts collaboration where silos exist. This transforms communication from secure exchanges into intelligence-driven decision flows.
Sovereign Control: Full custodial oversight remains in government hands. Administrators provision keys, define federation and roaming policies, and set the scope of AI functions. The platform adapts to sovereign rules and national priorities—never the other way around.
Operational Productivity: With an always-present digital officer capable of recalling prior meetings, referencing policies, and highlighting action points, officials reduce cognitive burden and gain continuity across leadership changes. This ensures decisions are sharper, faster, and more consistent.
Together, these capabilities establish a dual shield: one that protects communications against external threats while simultaneously augmenting governance with actionable intelligence. The result is not just secure messaging, but a policy-aware infrastructure that strengthens decision-making, accelerates inter-agency coordination, and ensures resilience in both peacetime operations and crisis response.
Proposed Solution: How It Works
The platform integrates defense-grade communication protocols with embedded agentic AI, deployed entirely within government-controlled infrastructure. It follows a zero-trust, sovereignty-first architecture, ensuring that sensitive data never leaves national oversight.
Encrypted Messaging & Groups
One-to-one and group communication is protected with end-to-end encryption. Within these channels, the AI functions as a contextual analyst—able to insert relevant insights (e.g., “This aligns with last quarter’s defense readiness report”) or flag risks in real time, without breaking encryption integrity.Secure Peer-to-Peer Channels
Direct exchanges between individuals or agencies are routed over the encrypted overlay network. AI-suggested responses are role- and policy-aware, ensuring consistency with national security directives and organizational protocols.Voice & Video Conferencing
Secure calls remain entirely within the sovereign perimeter. The AI transcribes in real time, highlights action items, and enforces data-sharing rules—reducing the risk of miscommunication and non-compliance.Custodial Key Management
Cryptographic keypairs are generated, issued, and managed solely by sovereign authorities. No vendor or external operator holds custody. Keys are treated as national assets, strengthening resilience against external compromise.Federation & Roaming Control
Each ministry or agency operates its own secure server. Leaders determine if, and how, users can roam across federated servers. The AI enforces these roaming and access rules dynamically, preventing unauthorized movement across the network.Agentic Oversight
Operating entirely within the encrypted perimeter, the AI observes interactions, identifies cross-departmental patterns, surfaces inter-agency connections, and adapts workflows to policy-defined constraints. Importantly, no data leaves sovereign control.
In essence, this system functions as a sovereign-grade communications backbone, with the AI acting as a trusted digital officer embedded in every exchange—shielding communications while simultaneously amplifying decision-making intelligence.
Operational Impact
Beyond efficiency, the impact is structural. Governments move from vulnerable, siloed, and overloaded systems to a secure, federated, intelligence-driven backbone. This shift reduces sovereign cyber-risk exposure, accelerates national crisis responses, and builds continuity across ministries—ensuring governance that is faster, more resilient, and trusted.
Metric | Before | After | Estimated Impact |
|---|---|---|---|
Communication Security | Reliance on vulnerable third-party apps | Military-grade encrypted overlay with AI oversight | Avoids breaches that cost US $4–14M per incident in government agencies |
Cross-Department Collaboration | Fragmented silos, duplicated work | AI-driven pattern detection and collaboration prompts | Unlocks productivity valued at up to C$700B in public sector efficiencies (Canada est.) |
Meeting Productivity | Manual recaps, scattered action items | AI auto-summaries and task flagging | Saves ~26 minutes per official daily → ~2 weeks of reclaimed time per civil servant annually |
Policy Compliance | Frequent policy and data-sharing violations | AI enforces compliance in real time | Reduces legal, regulatory, and reputational risk (millions per breach avoided) |
Workforce Efficiency | Cognitive overload from excess data | Personalized AI support tailored to role & mandate | Automates up to 41% of routine tasks, freeing thousands of man-days annually |
Beyond efficiency, the impact is structural. Governments move from vulnerable, siloed, and overloaded systems to a secure, federated, intelligence-driven backbone. This shift reduces sovereign cyber-risk exposure, accelerates national crisis responses, and builds continuity across ministries—ensuring governance that is faster, more resilient, and trusted.
Market Snapshot
The global secure communications market is projected to exceed $30 billion by 2030, with defense and government sectors as its primary growth drivers. At the same time, the rise of AI-augmented governance is creating a new category: platforms that combine cybersecurity resilience with operational intelligence.
Key Market Drivers
Rising Cyber Threats — Nation-state actors increasingly target sovereign communication systems as entry points for hybrid warfare, espionage, and disruption.
Data Sovereignty Mandates — Regulations now require in-country hosting, custodial encryption, and auditable oversight, limiting reliance on vendor-controlled clouds.
Operational Complexity — Ministries must coordinate across defense, health, infrastructure, and foreign affairs, demanding unified yet secure channels.
Current Vendor Landscape
Cloud Suites (Microsoft GCC High, Cisco Webex, Google Workspace) deliver compliance and integration but depend on vendor-cloud AI and telemetry outside sovereign control.
Secure Messengers (AWS Wickr, Wire) provide strong end-to-end encryption but lack policy-aware intelligence and cross-ministry coordination features.
Federated Platforms (Matrix/Element, Mattermost) support sovereignty and control, but agencies must DIY compliance, audit, and AI layers, which slows adoption.
High-Assurance Voice Tools (BlackBerry SecuSUITE, Thales Citadel) protect calls and text, but do not scale to government-wide collaboration or multi-modal workflows.
The Gap: No current solution integrates military-grade encryption, sovereign deployment, and embedded agentic AI into a single backbone. Governments are forced to choose between partial sovereignty, limited intelligence, or fragmented tools.
Our Differentiation: This platform directly addresses that convergence. By combining defense-grade overlay networks, custodial key management under national authority, and a policy-aware agent operating entirely within sovereign infrastructure, it provides both impenetrable security and decision-level intelligence. This positions it not just as another secure app, but as the category leader in sovereign communications modernization.
Recommendation: Hybrid Model
For governments, no single deployment model can meet both the sovereignty demands of national security agencies and the scalability needs of broader ministries. A hybrid-first architecture is therefore the most practical path forward:
On-Premise Sovereignty: Ministries with the most sensitive mandates—defense, intelligence, national security—operate fully on-premise servers. This ensures custodial ownership of infrastructure, encryption keys, and AI instances, with no external dependencies.
Secure Federated Cloud: Civil ministries and public-sector organizations leverage a secure cloud federation. Each entity retains its own encrypted domain, but cross-agency coordination is made possible through controlled federation. This accelerates scale without compromising encryption integrity.
Unified AI Oversight: The agentic AI operates only within the encrypted overlay, enforcing access policies, surfacing insights, and supporting decision-making. At no point does data leave sovereign boundaries or become accessible to vendor infrastructure.
This hybrid-first approach balances control, scalability, and resilience, ensuring governments can protect their most sensitive functions while modernizing communication across the wider public sector. Importantly, it positions the AI not as a vendor service, but as a trusted sovereign asset embedded in national infrastructure.
Roadmap
A structured nine-week proof-of-concept (PoC) provides a low-risk path for technical validation and stakeholder readiness. The roadmap ensures the platform is tested not only for functionality, but also for resilience, compliance, and operational fit.
Weeks 1–4: Foundation Setup
Deploy the encrypted overlay network and configure sovereign servers.
Stand up the agentic AI instance within the government-controlled environment.
Establish custodial key management protocols and federation boundaries.
Weeks 5–6: Operational Integration
Provision user groups across ministries.
Train the AI on national policies, procedures, and role-specific mandates.
Configure roaming rules and compliance enforcement mechanisms.
Weeks 7–8: Validation & Stress Testing
Conduct load testing to confirm performance under operational stress.
Run penetration tests and red-team simulations to validate security posture.
Measure AI accuracy in summarization, compliance enforcement, and policy alignment.
Week 9: Demonstration & Review
Deliver a live demonstration of military-grade security, cross-agency collaboration, and real-time agentic intelligence.
Engage stakeholders in scenario-based exercises to validate outcomes.
Collect feedback to define next-phase deployment strategy.
This phased approach minimizes technical and political risk, while building confidence across ministries. By the end of the PoC, stakeholders have tangible evidence of resilience, scalability, and intelligence augmentation in live government operations.
Market Opportunity & Strategic Host Partners
This platform is purpose-built for institutions where sovereignty, resilience, and intelligence are non-negotiable.
Defense & Intelligence Agencies — Require uncompromising protection against state-level adversaries, espionage, and hybrid warfare tactics.
National Ministries — Need secure, real-time coordination across critical portfolios such as health, infrastructure, foreign affairs, and energy.
Regional & Local Governments — Must modernize communication systems under resource constraints while facing persistent cyber threats.
Public-Sector Enterprises — Manage sensitive citizen or regulatory data subject to strict sovereignty and compliance mandates.
Strategic Positioning
This platform sits at the convergence of two megatrends: cybersecurity modernization and agentic AI adoption. Governments worldwide are under pressure to secure communications, comply with sovereignty mandates, and accelerate decision-making. Few existing solutions address all three demands simultaneously.
Partner Value
Strategic host partners and early adopters gain access to:
A high-barrier-to-entry market where trust, compliance, and sovereign control are decisive.
A category-defining platform that integrates military-grade security with intelligence augmentation.
Expansion potential into adjacent domains—regulated industries, multinational organizations, and defense contractors—where sovereignty and security are equally critical.
The thesis is clear: sovereign AI-secured communication is no longer optional; it is the new baseline. Engaging early ensures a role in shaping the standard for how governments communicate, decide, and govern in the digital era.
Conclusion: The New Baseline
Governments can no longer afford communication systems that compromise either security or intelligence. The threats are escalating, the costs are measurable, and the gaps in current solutions are undeniable. What is required now is a sovereign-grade communications backbone—one that not only resists state-level adversaries but also actively augments decision-making across ministries.
This platform establishes that baseline: military-grade encryption, sovereign custodial control, and embedded agentic intelligence operating entirely within national infrastructure. It transforms communication from a point of vulnerability into a strategic asset for governance.
The path forward is clear. Governments and strategic partners who adopt early will help define the standards of sovereign AI communication—and secure a position at the forefront of resilience, compliance, and operational intelligence.
📩 Reach out to us at [email protected] or book a discovery call here to explore partnerships.
About the Authors
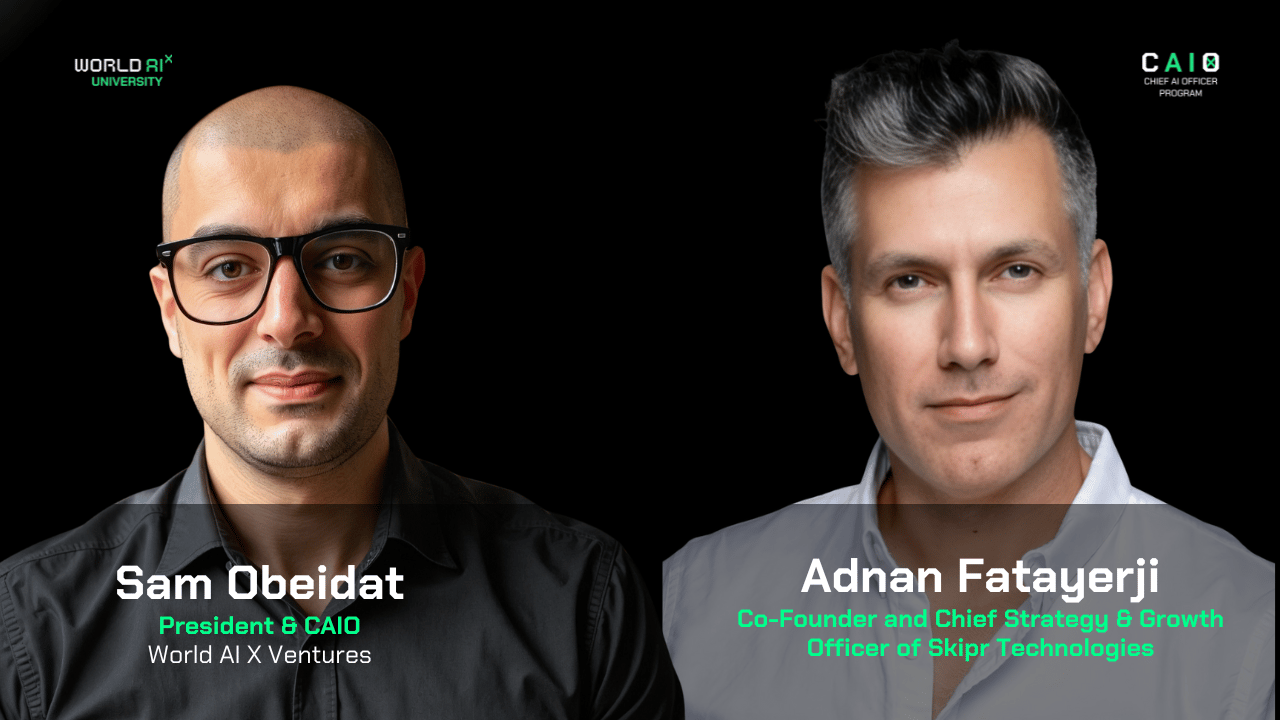
Sam Obeidat is a senior AI strategist, venture builder, and product leader with over 15 years of global experience. He has led AI transformations across 40+ organizations in 12+ sectors, including defense, aerospace, finance, healthcare, and government. As President of World AI X, a global corporate venture studio, Sam works with top executives and domain experts to co-develop high-impact AI use cases, validate them with host partners, and pilot them with investor backing—turning bold ideas into scalable ventures. Under his leadership, World AI X has launched ventures now valued at over $100 million, spanning sectors like defense tech, hedge funds, and education. Sam combines deep technical fluency with real-world execution. He’s built enterprise-grade AI systems from the ground up and developed proprietary frameworks that trigger KPIs, reduce costs, unlock revenue, and turn traditional organizations into AI-native leaders. He’s also the host of the Chief AI Officer (CAIO) Program, an executive training initiative empowering leaders to drive responsible AI transformation at scale.
Adnan Fatayerji is a leading figure in sovereign digital cloud infrastructure, recognized for co-founding and scaling pivotal ventures in decentralized internet and next-generation technologies. He co-founded Qamira (acquired by Kiswe Mobile), helped establish GIG Technology, and later co-founded the ThreeFold Foundation and ThreeFold Tech, building one of the largest decentralized and sovereign cloud infrastructures worldwide. Today, as Co-Founder and Chief Strategy & Growth Officer of Skipr Technologies, he is driving the transformation of AI-to-AI interoperability through non-static, ephemeral networks. His leadership includes spearheading high-profile initiatives such as piloting the world’s first decentralized sovereign cloud in the Middle East and Africa, while advancing data security and sovereignty across government and enterprise environments.
Sponsored by World AI X
The CAIO Program
Preparing Executives to Shape the Future of their Industries and Organizations
World AI X is excited to extend a special invitation for executives and visionary leaders to join our Chief AI Officer (CAIO) program! This is a unique opportunity to become a future AI leader or a CAIO in your field.
During a transformative, live 6-week journey, you'll participate in a hands-on simulation to develop a detailed AI strategy or project plan tailored to a specific use case of your choice. You'll receive personalized training and coaching from the top industry experts who have successfully led AI transformations in your field. They will guide you through the process and share valuable insights to help you achieve success.
By enrolling in the program, candidates can attend any of the upcoming cohorts over the next 12 months, allowing multiple opportunities for learning and growth.
We’d love to help you take this next step in your career.
About The AI CAIO Hub - by World AI X
The CAIO Hub is an exclusive space designed for executives from all sectors to stay ahead in the rapidly evolving AI landscape. It serves as a central repository for high-value resources, including industry reports, expert insights, cutting-edge research, and best practices across 12+ sectors. Whether you’re looking for strategic frameworks, implementation guides, or real-world AI success stories, this hub is your go-to destination for staying informed and making data-driven decisions.
Beyond resources, The CAIO Hub is a dynamic community, providing direct access to program updates, key announcements, and curated discussions. It’s where AI leaders can connect, share knowledge, and gain exclusive access to private content that isn’t available elsewhere. From emerging AI trends to regulatory shifts and transformative use cases, this hub ensures you’re always at the forefront of AI innovation.
For advertising inquiries, feedback, or suggestions, please reach out to us at [email protected].

